Water Rhyme Jiangsu, deserves your annual tourism
Jiangsu is a precious place blessed with rich materials and intelligent folks since the ancient times. It boasts magnificent palaces and private gardens. The scenic spots in Jiangsu is well-known of its water towns, Kunqu opera, gardens, brocades, etc. It presents the water rhythm of abundant rice and fishes everywhere. It is a good place to find something new else in each season in Jiangsu. It explicates picturesque scenery, for example, you can visit the garden and ancient town, enjoy the rain and drink tea in the Spring, watch lotus and prevent sunstroke in the Summer, visit lakes, eat delicious food and live in folk houses in the Autumn, and play snow, climb mountain and make blessings in the Winter.Jiangsu is a beautiful place worthy you for a whole year of travel.
Jiangsu is born with water
The magnificent Yangtze River, the vast Yellow Sea, the canal of stretches, the openness of the water network, the static flow under the bridge in the south of the Yangtze River, the various styles of water and the water with different temperament blend and complement in the landscape of Jiangsu, generating the unique spirit and character of grand,warm, soft and full of tension of Jiangsu.
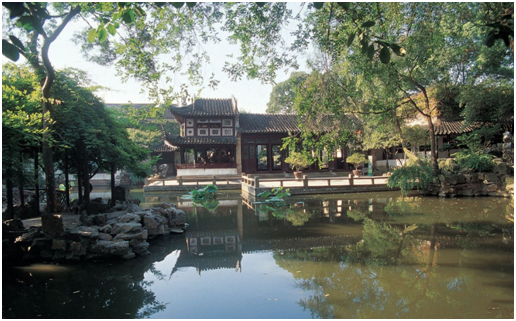
Jiangsu is a place of garden
Chinese gardens are a work of art. The ingenious combination of architecture, mountains and river, trees and flowers creates a flowing three-dimensional landscape painting, showing the intelligence and outstanding aesthetic sentiment of the Chinese nation. It is truly a shining pearl of traditional Chinese culture. Jiangnan Gardens are widely admired by the public for its distinctive features, while gardens in Jiangsu are of the best. Among China’s four major gardens, two are in Jiangsu, and the four major Jiangnan gardens are all situated in Jiangsu. All in all, what are the most unique and worthwhile gardens? Read this article and you’ll discover the six major gardens in Jiangsu that shouldn’t be missed!
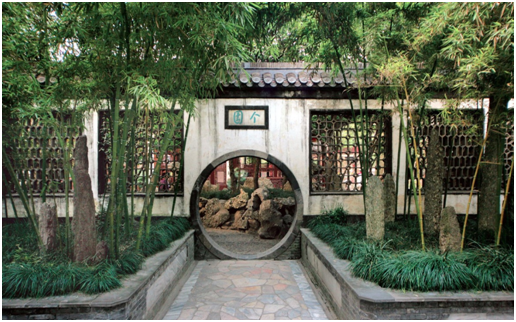
Lion Grove Garden|The King of Rockery
As one of the four famous gardens in Suzhou, the Lion Grove Garden is a representative of the Chinese gardens in the Yuan Dynasty, meanwhile is recognized as a UNESCO World Cultural Heritage Site and a Major Historical and Cultural Site Protected at the National Level. The name of the garden is derived from the shape of various rocks in it, which are said to resemble lions. The Lion Grove Garden was built by a Zen Buddhist monk Tianru, in memory of his master abbot Zhongfeng. The name also refers to the Lion Peak of Mount Tianmu in Lin’an, Hangzhou, where abbot Zhongfeng attained nirvana. The Lion Grove Garden combines the traditional gardening techniques with Buddhism ideology. With the introduction of western gardening techniques and ancestral hall into the garden, the Lion Grove Garden has become a temple garden integrating the essence of Zen Buddhism and the joy of gardening. Inside it, there are cultural landscapes of classical Suzhou gardens like pavilions, terraces, mansions, halls and galleries. It is also known as the “kingdom of rockery” for its lakes and mountains, peculiar rocks, deep and mysterious caves that are famous worldwide. There are plenty of beautiful and exquisite lakes and rocks, twisting and labyrinthine caves, which are called the “18 great sceneries of Taoyuan”. If you want to experience the most mysterious and linking maze, go to the Lion Grove Garden!
Humble Administrator’s Garden|Rejoice With Every Step of Your Way
Constructed in 1509 during the Ming Dynasty, the Humble Administrator’s Garden has a history of more than 500 years. With its fantastic layout of mountain, bamboo, pine trees and water, the garden is praised as “a model garden” and is the No.1 among the equally famous Chengde Mountain Resort, Lingering Garden and Beijing Summer Palace. As a UNESCO World Cultural Heritage Site and a Major Historical and Cultural Site Protected at the National Level, the Humble Administrator’s Garden is the only one in China to enjoy these four titles so far. The overall layout of the garden maintains the artistic styles of Ming Dynasty gardens, which are simple, vigorous and elegant. Centered on water, the garden comes with beautiful landscapes, exquisite pavilions, lush flowers and plants, meanwhile is full of poetic features and ambience of Jiangnan water town. The garden is divided into east, middle and west parts; while the east garden is pleasant and bright in pursuing of a pastoralism taste; the middle garden is the essence of the whole with well-arranged pavilions and halls, posing a sense of elegance; the west garden comes with quiet meandering paths and could bring you a pleasure of solitude. The Humble Administrator’s Garden is not the one to be missed if you come to Suzhou. Take a sip of tea in the garden, and enjoy the beautiful landscape there will surely be a rare and unforgettable experience.
Lingering Garden|Taoyuan Sweet Dreams
The Lingering Garden is also one of the four most famous gardens in China, well-known for its exquisitely-arranged constructions and numerous peculiar stones. The number of architecture in it ranks the 1st among all Suzhou gardens. The Lingering Garden as a whole is really particular about the layout of pavilions and towers, the cooperation of rockery and ponds, the contrast of flowers and trees, and different layers of close and distant views. The garden is divided into four scenic areas of the center, east, west and north by clusters of architecture. Each scenery is connected through windows and a corridor was built to connect all parts of the garden, where you can enjoy four different views of mountains and river, pastoral landscape, forests and courtyards. There are three unique highlights in the Lingering Garden, namely the Cloud Capped Peak, the Nanmu Hall, and the fish fossil, among which the Cloud Capped Peak is the most famed. The Cloud Capped Peak is a peerless piece of Taihu Lake stone with a combination of the characteristics of Taihu Stone – “thin, crinkled, leaky and transparent”. Like a dream of Taoyuan, the Lingering Garden is a detached but worldly place where you can stay, dine, relax, meditate and worship. The beauty of it needs you to immerse yourself in it to appreciate the proud strength of Taihu Stone, and to taste the exquisite romance of the ancients around pavilions.
Geyuan Garden|Bamboo Shadow of Four Seasons
Since the construction of gardens by salt merchants in Yangzhou back to the Qing Dynasty, there are many excellent and perfectly preserved classical gardens, of which the oldest, most complete, and most artistically valuable one would definitely be the Geyuan Garden. Now it has become a Major Historical and Cultural Site Protected at the National Level and the first group of national key parks. The Geyuan Garden is typically private residential retreat and is divided into the central garden, the southern residence, and a bamboo viewing area in the north. Renowned for bamboo stones, even the name of the garden “个” is the left part taken from the Chinese character “竹”, which means bamboo. Therefore, it could strike a chord with the various bamboos in the garden, and embody the temperament and mentality of the owner. Enjoy the beauty of four seasons one after another in the garden, this unique artistic technique is extremely rare in Chinese traditional gardens with a novel purpose and a tight structure, and is the only example among Chinese gardens. The Geyuan Garden is famous for the art of stacked stones, which adopts the method of “different mountains, different stones” to use bamboo stone, lake stone, yellow stone, and Xuan stone to create rockeries of four seasons, integrating gardening rules and landscape painting philosophies.
Master of the Nets Garden|Appealing Little Garden
The Master of the Nets Garden is a representative of medium-sized classical landscape gardens with artistic features and cultural values among Suzhou gardens. It is a model of “win more with less” and is known as “little garden, much essence”. If the Lingering Garden is a modest elderly person, the Humble Administrator’s Garden is a retired senior official, then the Master of the Nets Garden is no doubt a shy and adolescent Jiangnan girl. Centered on pool water, the whole garden is divided into 5 parts: the eastern residential area, the southern banquet area, the central pool area, the western inner garden and the northern study area. The annual Classical Night Garden in the Master of the Nets Garden is a classic travel product in Suzhou, so well-known both at home and abroad that it has been recommended by UNESCO as a specific tourist project. Every year from 4.1 to 10.31, performances such as storytelling, Kun Opera, folk dance, and folk music with rich Suzhou local characteristics are staged in various halls and pavilions. Come here to experience the oriental feast of all aspects.
Heyuan Garden|No.1 Garden in the Late Qing Dynasty
Built in the middle of the Qing Dynasty, the Heyuan Garden is a classical Chinese architecture, which integrates the essence of Yangzhou gardens and harmonizes with the elements of Western architecture. It is known as the “No.1 garden in the late Qing Dynasty”. There are 4 “No.1 in the world” hidden in the garden. The “No.1 gallery” refers to the complex corridor connecting towers in the western garden. The “No.1 window” refers to the flower windows on the gallery, which have various shapes like folding fans, vases, plum blossom, etc. Looking out of the window, the window is like a picture frame to capture different views from different angles. The “No.1 pavilion” refers to the Shuixin Pavilion in the pond center of western garden. Designed for garden owners to enjoy opera, singing, dancing and to appreciate the scenery, the Shuixin Pavilion is the only water theater in China. The “No.1 mountain” is the Pian Shi Shan Fang (片石山房), the only masterpiece of garden and stacked stone by Shi Tao, a great painting artist in the early Qing Dynasty. The organic harmony of the corridors, halls, pavilions, rockery and water will give people an artistic conception of “stillness in motion, motion in stillness”.
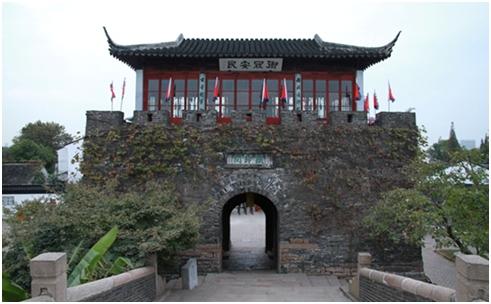
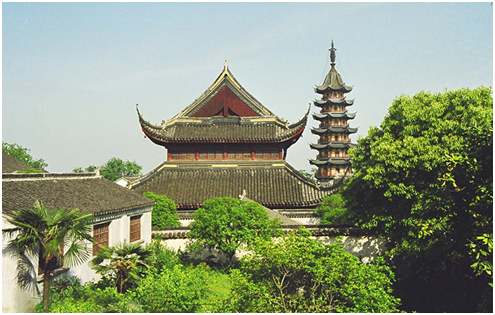
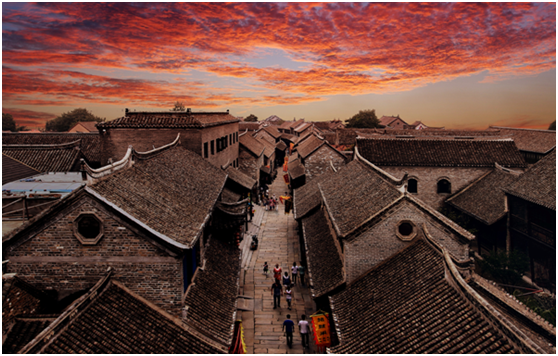
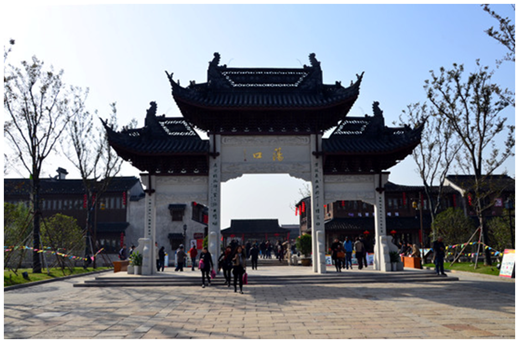
Jiangsu is a place of ancient town
A catalogue of ancient towns stand quiescently on the water, flowing and standing still forever. The ancient streets are hidden in the town with black bricks, and there are several old-style tea houses along the street. Bridges, flowing water and water towns have captured the hearts of many tourists, what is the most worthy of ancient towns for you to Pick? Today, I will recommend you the top ten ancient towns in Jiangsu to make you have a deep understanding of Jiangsu and ancient towns. Let’s Go!
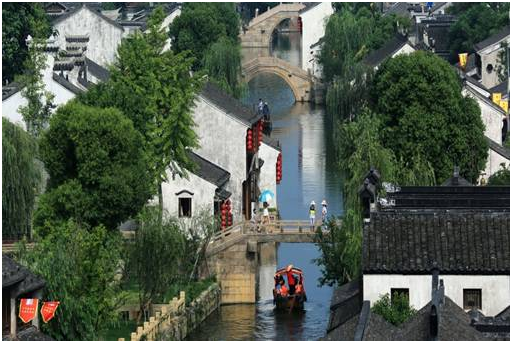
Tongli Ancient Town – “Venice of the East”
Tongli is built in the Song Dynasty and located in Wujiang District, Suzhou, Jiangsu Province. With a history of more than 1,000 years, it is one of the six famous water towns in Jiangnan and the only ancient town with a UNESCO World Heritage site. The town is surrounded by water, divided into 7 small islands by 15 rivers, and connected by 49 ancient bridges. Every house in the town is faced with water and has easy access to boats, forming its unique scenery. It is really amazing and beautiful to wander in this Jiangnan water town with blue stone paths, white walls, small bridges and lotus pond.
Zhouzhuang Ancient Town – China’s No.1 Water Town
Zhouzhuang is a simple and quiet water town located in Kunshan, Suzhou. It came into being because of water and is surrounded by rivers. Its streets are close to rivers and connected by bridges. Built in the Northern Song Dynasty, the town has a history of over 900 years and features a rich Wu culture. Zhouzhuang has been regarded as the treasure of the oriental culture with its beautiful scenery of water town, unique cultural landscape and folk custom.
Jinxi Ancient Town – Home to Privately-owned Museums in China
Jinxi, an ancient water town in the southwest of Kunshan, Jiangsu Province, has a history of over 2,500 years, featuring many lakes, water lanes and ancient bridges. It is a scholarly town boasting a great number of talents in the past one hundred years, including over 100 students studying abroad, over 200 professors, Astronomer Zhu Wenxin, Academician of Chinese Academy of Sciences Chen Huagui and Academician of Chinese Academy of Sciences Qin Guogang. Jinxi is known for collections and has 15 private collection museums, which have become a new highlight and are worth a visit.
Luzhi Ancient Town – No.1 Town among Water Towns in China
Luzhi is located in Wuzhong District, Suzhou, and has a history of 2,500 years. Many people may mistake “甪直” as “角直”. Actually it is lù zhí. With a lot of small bridges and water lanes, people in the town have easy access to water. Known as the “Museum of Ancient Bridges in China”, Luzhi is surrounded by Cheng Lake, Wanqian Lake, Jinji Lake, Dushu Lake and Yangcheng Lake. Additionally, Wusong River, Qingshui River, Nantang River, Jiepu River, Dongtang River and Dazhi River are crossed within the town.
Fengqiao Ancient Town – China’s No.1 Town in Ming and Qing Dynasties
The poet Zhang Ji from Tang Dynasty depicted Maple Bridge in his famous poem Mooring at Night by Maple Bridge, making Maple Bridge a popular scenic spot. Situated in Huqiu District, Suzhou, Jiangsu Province, Fengqiao town is at the intersection of an ancient post road and Maple River, made up of Maple Bridge Street and Hanshan Temple Lane. Now Fengqiao has become a relatively large and amazing scenic area with numerous historical sites, rich Wu culture and profound cultural background. It is not only a good choice for sightseeing, shopping and relaxation, but also a good place to learn about Suzhou.
Mudu Ancient Town – The Only Ancient Town Famed as China’s Garden Town
Mudu, located in the west of Suzhou and on the shore of Taihu Lake, has a history of more than 2,500 years, with beautiful scenery and rich resources. It is surrounded by the famous mountains in Wuzhong, such as Mount Tianping, Mount Lingyan, Mount Lion and Mount Qizi. Mudu is famed by the contemporary people as “No.1 Town in Wuzhong” and “the most beautiful town in Jiangnan”. It is said that Emperor Qianlong of the Qing Dynasty went to Jiangnan six times and visited Mudu six times, which shows the unique charm of this place.
Qiandeng Ancient Town – Hometown of Gu Yanwu and Birthplace of Kun Opera
Qiandeng is located in Kunshan and has a history of 2,500 years. It is the hometown of Gu Yanwu and also the birthplace of Kun Opera. The town features white walls and black tiles. Compared with other ancient towns in Jiangnan, it is a simple and relatively small town without a big name, commercialization or modern recreational facilities, making it a good place to enjoy the beauty of ancient towns in Jiangnan.
Yaowan Ancient Town – “An Amazing Water Town in Northern Jiangsu”
Yaowan is located in the southwest of Linyi, Xuzhou, Jiangsu Province, and at the intersection of located Beijing–Hangzhou Grand Canal and Luoma Lake. Built in 618 (Tang Dynasty) and with history of over 1,300 years, the town is known for facing the sea in the east, Xuzhou (Pengcheng in ancient times) in the west, Huaisi in the south and Mount Tai in the north, and also known as “the golden triangle in the golden waterway”, “An Amazing Water Town in Northern Jiangsu” and “small Shanghai”. It is a stable and elegant town, featuring ancient houses, streets, shops, wharfs and historical sites, which forms its culture. Yaowan is the true portrayal of the ancient canal culture in the folk heritage.
Dangkou Ancient Town – China’s Town of Photography (in Ehu Town)
Dangkou is located in Ehu Town, the southeast of Xishan District, Wuxi, Jiangsu Province, facing Taibo Tomb and the Tombs of the Nobles of Yue Kingdom to the west, Suzhou and Changshu to the east. The town has crisscrossing waterways nearby, many lakes, small bridges and elegant environment, with Ezhun Lake to the east, Nanqing Lake to the south, Caiwan Lake to the north and Sushe Lake to the west. Dangkou is a beautiful and famous historical water town in Jiangnan, known as “small Suzhou” and “Silver Dangkou”.
Zhenze Ancient Town – Hometown of China’s Silk
Zhenze is located in the southwest of Wujiang District, Suzhou, Jiangsu Province. With a history of over 2,000 years, it is a good place featuring not only small bridges and water, but also elegant and beautiful scenery. Zhenze town is the home to China’s well-known silk, where you can pick mulberry, pick mulberry leaves to feed silkworms and take baby silkworms home.
江苏是荷香满园的的江苏 Jiangsu is a place of scented lotus
The grace of Jiangsu is unique and its lotus is pure and sanctity. What a comfortable life for you to drink tea and watch lotus in the boat and listen to Kunqu opera and see wonderful landscape in the garden!Nanjing Xuanwu Lake, Mochou Lake, Yangzhou Slender West Lake, Suzhou Zhuozheng Lake……the next will lead you to visit our rivers and lotus!
Xuanwu Lake, Nanjing
Speaking of the best places to appreciate lotus, Nanjing, one of China’s eight famous spots for lotus-viewing, must be on the list. The vast and spectacular landscape of infinite lotuses is everywhere. Meanwhile, the combination of floating boats, flying dragonflies and blooming lotuses is there to offer a poetic picture. During the 2018 Xuanwu Lake Lotus Festival from June 16 – Aug 22, come with your friends to have a romantic date with this beautiful scenery of lotus!
Mochou Lake, Nanjing
The most characteristic lotus flower at Mochou Lake is the one that is wrapped by another, which is a very rare species among its kind. This type of lotus is usually pink, the petals large and round with a big flower wrapping a small one and the two outer layers of petals forming a flower pattern. The tips of flower fold slightly for protection and flowers are wrapped in the middle again.
Slender West Lake, Yangzhou
The growing of lotus has been a popular tradition in Yangzhou since ancient times, while the Slender West Lake is undoubtedly the nation-famous spot for viewing it. In the scenic area, not only can you enjoy the delicate lotuses planted in pools and big jars, but also immerse yourself in the fragrance of lotus with every step of your way. Take a stroll alongside lotus is the most romantic thing to do!
Humble Administrator’s Garden, Suzhou
Jiangnan gardens are like young girls in a boudoir with different dressing at different times. In summer, the garden comes with awesome sceneries as the ponds full of lotus leaves. Walking on the bridge is like moving in a cluster of lotuses. The picture as a whole will surely make the experience unforgettable.
Hongze Lake Wetland Park
In July, the lotus flowers in the wetland park bloom one after another in the Daguan Garden, Jiuyue Lake and Qianhe Garden. The Qianhe Garden is located on a small island in the southwest of the wetland park. There is a large pond full of lotus flowers in the middle of the island, forming a unique picture with islands and lakes existing altogether. The most unique landscape is still the “widespread wild ducks and lotus roots” of Hongze Lake. The playing ducks in the middle of the pond add more to the vitality of the lotus garden.
You can travel along with “water”and experience the pleasure by “rhyme”, and feel the fresh “water life” in Jiangsu. Nanjing’s Six Dynasties, Suzhou’s ancient town and gardens, Wuxi’s Taihu scenery, Changzhou’s theme park, Zhenjiang’s temples and mountains, Yangzhou’s Han and Tang culture, Taizhou’s national quintessence, Nantong’s Jiangtao tide, Yancheng’s red history, and the rare birds beast, the sealand of Lianyungang, the former residence of the great people of Huai’an, the pastoral scenery of Suqian, the relics of Xuzhou during Qin and Han dynasties…
Just come to Jiangsu!